At the end of last week, on the morning of May 12, the virtual world shuddered: virus-extortionist WanaCrypt0r 2.0 (aka WCry) attacked computers in many countries of the world.
The first to hit were hospitals in
According to experts, this is a typical extortion virus that gets to computers through email services with spam. When the letter is opened, the program that encrypts all files on the hard disk is activated, and the offer to send a certain amount in bitcoins to a certain account appears on the desktop. By the way, the malicious program was known as back as in February, but this is its most powerful strain.
World extortionist
It is interesting that the aim of the attackers was to a greater extent the whole organizations, and the main blow was reportedly taken by the state bodies of
The All-Russian base of the Federal Registration Information System was also attacked on the same day, which remained unnoticed for 40–45 minutes.
It is possible that the attackers got access not only to the registration data of citizens and vehicles, but also to the bailiffs' base that was uploaded to it. Russian law enforcers told the media how the attackers could use the downloaded vehicle data. Firstly, these are machines — duplicates, and secondly, it will be more convenient for car thieves to look for cars ordered to them.
And now let’s assume that this virus is just a test ball for checking the efficiency of local IT professionals and how securely protected government systems are. Does this version have the right to exist? Why not?
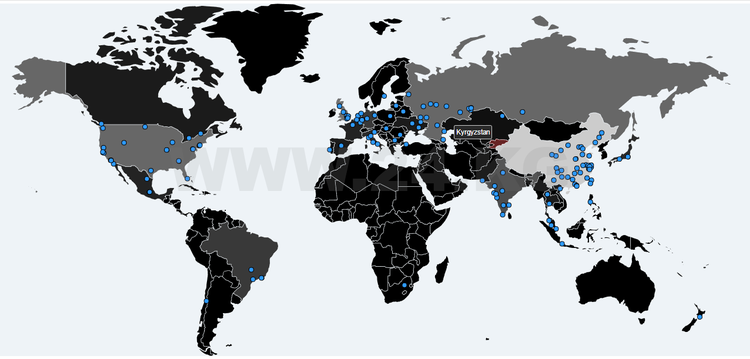
Moreover, the interactive map of virus infection showed:
Test ball
The country’s main elections will take place in
The system exists in non-contact automatic mode. The server serves to obtain information from 2,500 polling stations, it does not form the results of elections.
Nurzhan Shayldabekova
The CEC Chairwoman also admitted that during the inter-election period, CEC servers were attacked by hackers, but the current level of protection allowed protecting them. The head of the commission suggested that there was a test hacking attempt before the election day. Nurzhan Shayldabekova with the resistance of a partisan was silent about whether she and members of the Central Electoral Commission had access to server equipment, but admitted that two employees had such a right.
In general, many mistakenly believe that the physical presence of a person in the server room is necessary to interfere with the operation of an intelligent system. So, to demonstrate the equipment, CEC issued an order to form a commission of representatives of the media. Loudly announcing the names of its members, the operators took them to the coveted premises, but strictly forbade taking mobile phones and cameras. Journalists were also shown a journal of visits to the place of information.
To change the operation of the system, and also to completely paralyze it, it is not necessary to enter this specially guarded room.
And all sorts of hacker attacks on government servers is a proof.
Test data collection?
By the way, there is a recent example. The day before the presentation of the Central Election Commission, 24.kg news agency reported that the government portal of electronic appeals of citizens kattar.kg was hacked, and the database of the site was deleted. Could you imagine, the applications of citizens from the government portal were deleted!
The press service of the government added that «the staff of the department of letters and reception of citizens, as well as specialists of the Office of the President and Government of the
By the way, domestic websites are mostly attacked by hackers from
The websites of the Ministry of Internal Affairs, the National Olympic Committee, the government media Kyrgyz Tuusu and Slovo Kyrgyzstana, the human rights movement Bir Duyno-Kyrgyzstan, Atatürk-Alatoo International University, car dealers, consulting companies, online shops and other organizations failed to withstand the hacker attacks.
According to Vladislav Tkachev, director of IT audit at the international company Baker Tilly Bishkek, before talking about providing government agencies with an appropriate level of information security, it is necessary to clarify exactly what requirements this level corresponds to.
Whom will we look to?
«Unfortunately, the legal field of the
Neither the Administrative Code nor the Criminal Code of the Kyrgyz Republic stipulates responsibility for improper information security (IS), or inappropriate storage of data that led to their loss, inaccessibility or disclosure.
Vladislav Tkachev
In his opinion, this is one of the reasons why the level of information security in the country is extremely low, and due attention is not paid to its increase.
On the other hand, there is international experience in risk assessment, management of information security processes and data protection, within which all the necessary standards, recommendations, best practices and requirements have already been developed. Moreover, all these decisions are regularly reviewed, supplemented and improved depending on the changing landscape of cyber threats in the world.
«Commercial companies, without waiting for the adoption of laws and regulations in this area, have been using this experience for a long time, introducing advanced processes and requirements for protection of their data. And, as statistics show, the commercial sector had made the right choice. Speaking about the security of state bodies and their systems, it is necessary to understand what requirements they meet. And proceeding from this, we must draw a conclusion on the level of security of our data," Vladislav Tkachev added.
The state body must pass voluntary certification for compliance with the requirements of an international standard (for example, ISO / IEC 27001: 2013) or obtain an independent auditor’s opinion on compliance with such requirements.
Antidote
According to Tkachev, information security is not the result, it’s a process, and it is not enough to buy expensive data protection equipment, install an antivirus and, at best, develop several documents on information security. But exactly this happens: the money is being spent, the management notes that the item of «Improvement of IS» plan has been fulfilled, and everything stops there.
Vladislav Tkachev believes that, first of all, it is necessary to create conditions under which the work of all production processes without exception becomes subordinate to the goals of providing information security. Also, one should ensure constant monitoring of processes and their correct work. And, finally, one should constantly assess and re-evaluate the risks, take measures to reduce them to an acceptable level.
«For example, an expensive solution to prevent data leaks will be absolutely useless if for 2,000–3,000 soms you can bribe an operator and get all the necessary information without hacking of the system. Or another example: the penetration of viruses in the network of state bodies becomes possible when officials and civil servants manually activate attached files in e-mails with questionable or suspicious content," Vladislav Tkachev said.
«According to our estimates, hacking of websites occurred for a trivial reason — because of the use of vulnerable software," the expert said. «If there was a process in the departments for the regular and timely updating of the software, then this could be avoided.»
«By the way, the sensational attack of the extortion virus was successful due to the fact that users neglected recommendations and did not update their operating systems on time," the expert added.
As experience shows, the vector of attacks has shifted. And if before hackers attacked exclusively information systems, now the most effective method of penetration is the application of social engineering methods aimed at «hacking» a person. And such attacks can not be prevented by hardware or software.
Kyrgyzstan is saved not because «our system is reliably protected», but because of the fact that «we» are uninteresting to the hackers, not interesting so far.
Newcomers are simply exercising by hacking Kyrgyz websites. And this is eloquently demonstrated by the fact that from January 1 to May 15, 776 websites belonging to various commercial companies, individuals and state agencies have been hacked in
According to the information of the IT audit department of the international company Baker Tilly Bishkek, on average, 20 websites are successfully hacked every five days in the country, every tenth is hacked repeatedly.
So, before the upcoming presidential election, the specialists of the agencies involved in this event need to secure the information system as much as possible not to have a pale appearance.
It could happen that some wise guy will decide to practice on the electoral system of
One part of the specialists works for a private person and will never agree on the minor sum the state agency can offer them. Other bright minds left the country and are unlikely to return. By the way, does the State Committee for National Security have a list of the people capable of working in cyberspace professionally? If not, there is no point in talking about it at all.